Blogs
Cybersecurity Tips

Challenges of Securing Operation Technology
Operational Technology (OT) is often a second thought in the average person’s mind. Many people do not understand how OT works, what is needed for

Under Attack: Cyber Threats Targeting Canada’s Universities
On March 24, 2024, students and members of staff at the University of Winnipeg attempted to log in to their university system, only to find

The Invisible Threat of Identity Theft
How to manage this silent danger Identity theft is one of the most deceptive and damaging threats to both individuals and businesses. Unlike stolen

Navigating ePHI Compliance Across Borders
Understanding HIPAA, PIPEDA, and PHIPA and how they interconnect A routine hospital visit often involves handing over seemingly trivial data that we don’t give a

Using AI Safely in the Workplace
How to Integrate AI in the Office Responsibly Whether permission is granted or not, many employees now rely on AI technology to complete routine tasks.

AI in Healthcare Compliance
How does HIPAA work with Smart Hospitals The integration of AI in healthcare has been widespread across several industries, and the healthcare sector is no

Navigating AI Compliance: Strategies for 2024 and Beyond
As artificial intelligence (AI) continues to revolutionize industries, organizations face the dual challenge of harnessing its potential while ensuring compliance with evolving regulations. In 2024,

All about penetration testing and why it is so important
Penetration testing, also known as pen testing or ethical hacking, is a critical component of any organization’s security strategy. It involves simulating attacks from malicious
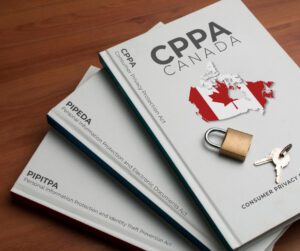
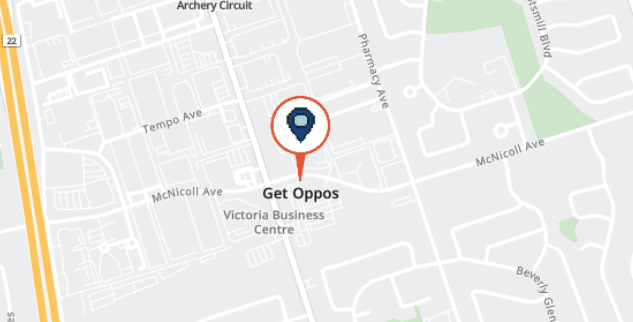
What is PIPEDA and its purpose?
The Personal Information Protection and Electronic Documents Act (PIPEDA) is a cornerstone of Canadian privacy law, governing how private-sector organizations handle personal information during commercial